First thing we need to do is get rid of the default KDE bluetooth manager, because quite frankly it sucks. It will not allow you to add a bluetooth device if it is not an Input device like a mouse or keyboard.
sudo apt-get remove kbluetooth
Now we have to install a bunch of packages:
sudo apt-get install blueman bluex bluez-btsco bluez-COMPAT pulseaudio-* paprefs paman padevchooser
That's a lot of stuff.. I'll attempt to explain:
blueman is the replacement for kbluetooth, and will let you pair up any kind of device.. the bluez packages contain the bluetooth modules you will need, and pulseaudio is required as well because ALSA (The default sound system in kubuntu) does not do bluetooth audio very well.
It's a good idea to reboot your system after installing all these packages.
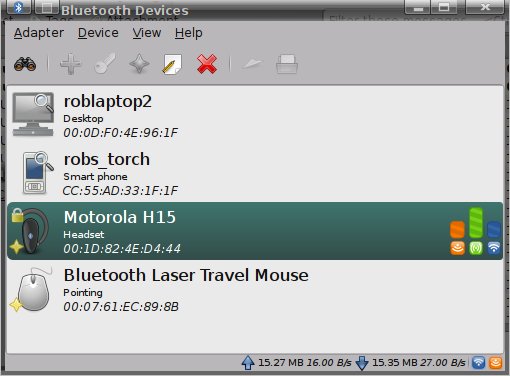
Once you have all the above packages installed you will need to pair up the headset with your bluetooth stack.
Make sure your bluetooth dongle / adapter is enabled and turned on
Put the headset into pairing mode and launch blueman-applet, either from the CLI or the kde menu, and click on the binoculars to search for a device, once it appears, select it and choose the Setup Assistant (Pencil and Paper icon) The pairing steps are pretty straight forward.
Next we need to make sure pulseaudio sees your newley paired headset:
pavucontrol
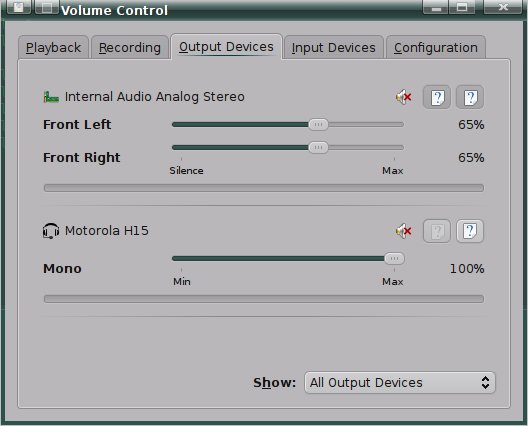
You should see your headset listed here on both the Output and Input devices tab
Next we need to get both the sound device name (sink) and the microphone device name (output) for your headset:
pactl list
Should generate a bunch of output. You are looking for two sections, sink and output that contain bluez in the name like this:
This is the Speaker for your headset, you can identify the name by the mac address for your headset (Yours will be different than shown here)
Sink #3
State: SUSPENDED
Name: bluez_sink.00_1D_82_4E_D4_44
Description: Motorola H15
Driver: module-bluetooth-device.c
Sample Specification: s16le 1ch 8000Hz
Channel Map: mono
Owner Module: 19
Mute: no
Volume: 0: 100%
balance 0.00
Base Volume: 100%
Monitor Source: bluez_sink.00_1D_82_4E_D4_44.monitor
Latency: 0 usec, configured 0 usec
Flags: HARDWARE HW_VOLUME_CTRL LATENCY
Properties:
bluetooth.protocol = "sco"
device.intended_roles = "phone"
device.description = "Motorola H15"
device.string = "00:1D:82:4E:D4:44"
device.api = "bluez"
device.class = "sound"
device.bus = "bluetooth"
device.form_factor = "headset"
bluez.path = "/org/bluez/1250/hci0/dev_00_1D_82_4E_D4_44"
bluez.class = "0x200404"
bluez.name = "Motorola H15"
device.icon_name = "audio-headset-bluetooth"
This is the Microphone:
Source #7
State: SUSPENDED
Name: bluez_source.00_1D_82_4E_D4_44
Description: Motorola H15
Driver: module-bluetooth-device.c
Sample Specification: s16le 1ch 8000Hz
Channel Map: mono
Owner Module: 19
Mute: no
Volume: 0: 100%
balance 0.00
Base Volume: 100%
Monitor of Sink: n/a
Latency: 0 usec, configured 0 usec
Flags: HARDWARE HW_VOLUME_CTRL LATENCY
Properties:
bluetooth.protocol = "hsp"
device.intended_roles = "phone"
device.description = "Motorola H15"
device.string = "00:1D:82:4E:D4:44"
device.api = "bluez"
device.class = "sound"
device.bus = "bluetooth"
device.form_factor = "headset"
bluez.path = "/org/bluez/1250/hci0/dev_00_1D_82_4E_D4_44"
bluez.class = "0x200404"
bluez.name = "Motorola H15"
device.icon_name = "audio-headset-bluetooth"
bluetooth.nrec = "1"
Note: Do not pick the names with the word "monitor" in them
Next we need to create a file in our home directories:
vim ~/.asoundrc
with the following contents:
pcm.<You_pick_devicename> {
type pulse
device <devicename_from_output_of_pactl_list>
hint {
description "<your_description>"
}
}
pcm.<you_pick_mic_devicename> {
type pulse
device <devicename_from_output_of_pactl_list>
hint {
description "<your_description>"
}
}
This file will contain a mapping from a virtual ALSA audio device to the pulseaudio device that coresponds to your bluetooth headset. For example, my config:
pcm.h15_sink {
type pulse
device bluez_sink.00_1D_82_4E_D4_44
hint {
description "Motorola H15 - Speaker"
}
}
pcm.h15_source {
type pulse
device bluez_source.00_1D_82_4E_D4_44
hint {
description "Motorola H15 - Microphone"
}w
}
My workplace has an Asterix PBX, so I use Twinkle for my IP softphone. All that remains to do is set up Twinkle to use the config above. Launch Twinkle and hit edit --> System Settings --> Audio
For Speaker, choose "ALSA: other device" and in the box below, put the name of the "sink" device you configured above.. (In my case h15_sink)
For Microphone, choose "ALSA: other device" and in the box below, put the name of the "source" device you configured above (In my case h15_source)
When I installed Skype, it defaulted to the pule audio driver, and my headset just worked out of the box.
After that, fire it up and enjoy.
]]>